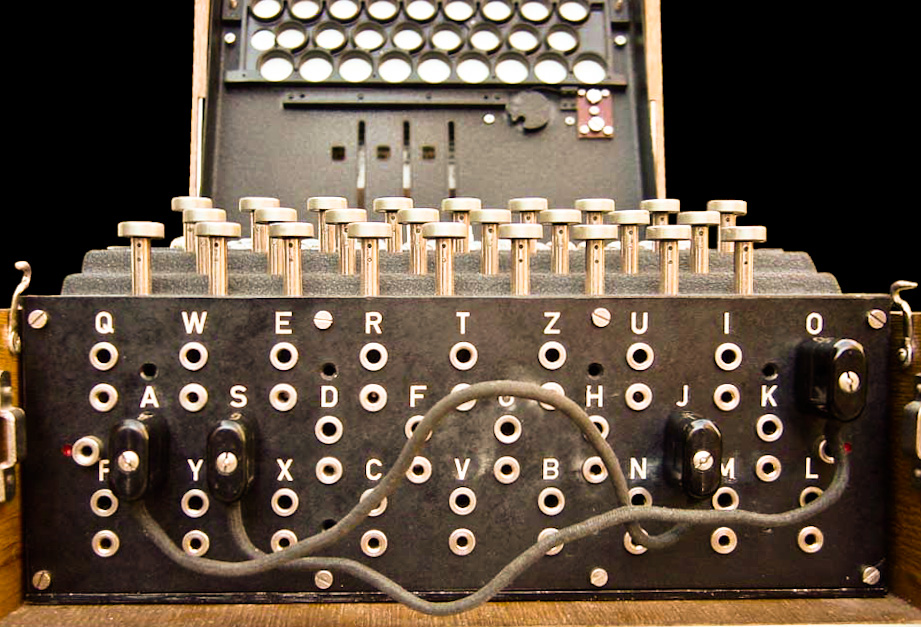
Human Isolated Credentials as Policy
“I’ve got news for Mr. Santayana: we’re doomed to repeat the past no matter what. That’s what it is to be alive.” - Kurt Vonnegut Jr Whether its passwords to access external service, API keys, or other forms of credentials, we not only know that our applications need them, but we also know that they are in reality, highly likely to be exposed beyond the security boundaries we define for them. Most commonly the exposure will come from a human error. Keys committed to a GitHub repository 1,2, incorrect permissions on an S3 bucket 3,4,5 and so on.
Practical AWS for Large Organisations
Practical AWS for Large Organisations Table of Contents Overview 1.1. Service Catalogs 1.2. Automated Push Security 1.3. Standardised Support Wrapper Patterns 1.4. Alignment to Industry Standards 1.5. Scalable Account Management Accounts Structure 2.1. Landing Zone Master Organisation Account Cross-Account Management Account Shared Services Account Security and Audit Account Billing Account Pipelined Data Flows and Reactive Architecture Central Services 4.1. Base Infrastructure 4.2. Persistence Infrastructure 4.3. Service Infrastructure Deploy pipeline DNS Routing Load Balancer Routing Compute Pluggable Compute Solutions 5.1. Standard Quick Start Products 5.2. Commercial Marketplace Products 5.3. Custom In-House Products CI/CD Pipelines Solutions Overview There are a number of components that enable business AWS management at scale. Key is to bring them together in a consistent and coherent way through combining and enhancing AWS templates and professional services solutions. Those that are most useful for scaled management such as multi-account landing zones and cross-account management are available but not necessarily fully automated. However, using these as the basis of our scaled strategy allows building on good foundations for future improvement. Looking at the AWS account landscape as a whole we can break it down into a handful of important areas.
Automated Token Generation with Cloudformation Custom Resource Lambdas
Automated Credential Token with Cloudformation Custom Resource Lambdas The automated token template, [][1]
Solving Once with AWS Service Catalog
Developing Cross Organisational Cloud Solutions at Scale with AWS Service Catalog What the problem looks like Large organisations can often develop into isolated fragments of technical development over time. Teams working in one part may not be aware of what others are doing, even in the same building. From a technical standpoint the result is at best sub-optimal, resulting in duplication of work and reinvention of the wheel. Velocity is low as disparate teams build cloud infrastructure foundations again and again before starting on their actual projects.
ECS Parameter Store Synchroniser
Working with credentials within ECS and passing them around is not entirely straighforward. As one way of doing this, this solution bases all environment variable storage in the AWS Parameter Store, then automatically synchronises them with the running tasks in a set of specified ECS clusters and tasks. [][1]
From Bricks to Cities - Government at Scale on AWS
Moving government into the cloud turned out all about asking the right questions. The arguments against had been around for many years, and put doubt in the minds of those with more traditional attitudes to IT. Is the cloud secure, is data safe? Many of these questions were the result of the disparity in experiences and conceptual understanding of the change between running in-house servers and running cloud infrastructures. Luckily as time has moved on, understanding and experience has moved in tandem, and these questions are not as commonplace. As we go from asking whether or not cloud technologies are the ‘right way’ for government we begin to ask more practical questions, such as, what is the ‘good way’ to run government in the cloud?
Deploying AWS Elastic Beanstalk
This template deploys elastic beanstalk into a new VPC, specifically amazons VPC architecture quick start VPC [100]. The instances are deployed into private subnets and the Application Load Balancer (ALB) into public subnets. A route is created into the service with the format <service_name>.<domain_name>. The template can utilise all of the standard beanstalk backends, ruby, python, node, docker, ecs, tomcat, go, php, dotnet. AWS Certificate manager backed HTTPS can be enabled but this will require an existing MX record in the hosted zone. [101] There are also options to add Elasticache and some other options. In the case of AWS components such as Elasticache, some standard environment variables are also created such as REDIS_URL. [Elastic Beanstalk into a new VPC][1] [][10]
Quick Sites with AWS S3 and CloudFront
[][2] Sometimes we just need a quick static site rather than anything elaborate, for example when we want to setup maintenance pages and Route 53 DNS failover for sites. Particularly for a maintenance or backup site we’re likely going to be using it for when there are availability zone or region problems in AWS. S3 static sites are incredibly easy, but we set SSL certificates on the site, which is not ideal.
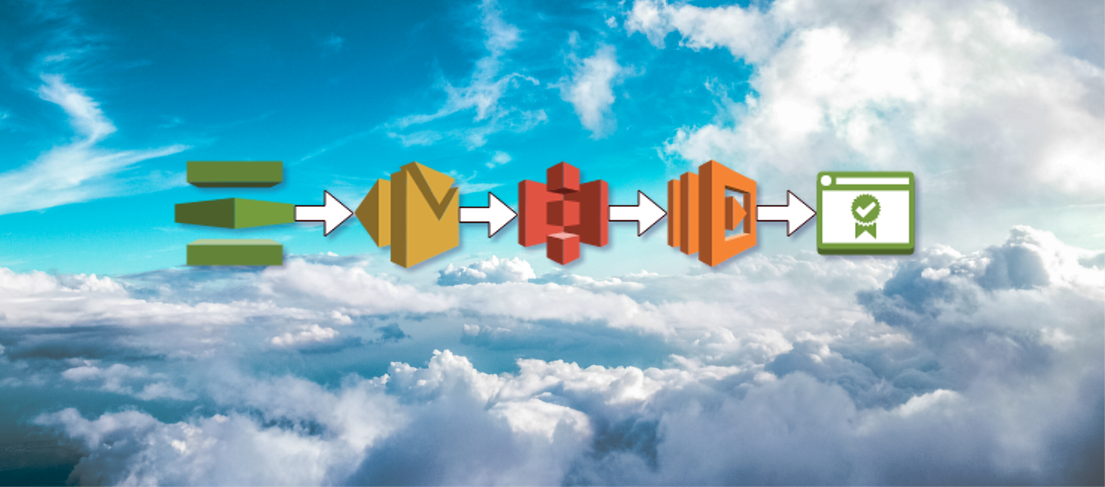
AWS Certificate Manager Pipelining
[][5] This post will walkthrough automating AWS Certificate Manager validation through a Simple Email Service (SES), S3 and Lambda pipeline.
Agent Self-Organisation in the Cloud
In the field of modern cloud operations, multiple services continuously run on many different platforms, across a broad spectrum or hardware, network, and software environments. Broadly, they can be briefly summarised as having the following properties,
Security Update Strategies for Ubuntu AMI
We need to get security updates onto instances on live AWS services. So, whats the best strategy? If we’re using the Amazon Linux AMI, then we security updates are automatically applied on the initial boot of the AMI. So if we cycle our instances, we get a freshly updated EC2 instance.
Minimum Downtime instance cycling
The goal here is to implement an instance cycling task, resulting in all current instances being replaced with new instances with no downtime. When working with auto-scaling groups, its important to remember that the auto-scaling group is in control! Simply rebooting will most likely spook the scaling group into replacing the downed instance.
Designing for Sustainability in an AWS Infrastructure
What are the key concepts that define what we mean by a sustainable service on AWS?
Transferring RDS Data Between Containers on Different AWS Stacks
Quick bunch of notes on moving data between container on AWS using RDS. Here we have 2 stacks, each with a container sitting on an EC2 instance. The container is running a simple rails application connected to RDS specified in the DB_HOST environment variable. There are other shortcut ways to do this but this is the ‘pretty straightforward’ way 🙂
Introduction to Cloudwatch
Some slides from an investigation into migrating to using Amazons Cloudwatch. Quick summary, Create metrics on Cloudwatch logging streams and alert on them, eg, number of 500’s in a minute You get basic free metrics from AWS, custom metrics are pretty easy to setup You have access to plenty of AWS specific metrics and triggers They are well integrated with other AWS stuff so you can do more advanced Lamda processing But, is it enough to moving away from your custom ELK/graphite type stack? Cloudwatch slideshow